For emerging security teams that don’t need overly complex tools, Sumo Logic Cloud Security Analytics addresses key security challenges without the higher cost or added complexity of enterprise-grade tooling.
Sponsored by Sumo Logic

The recent trend of state-sponsored hackers targeting small businesses is just one example of how SMBs (small-medium businesses) and organizations without a dedicated SOC (security operations center) face many of the same security challenges that enterprises face.
That comes at a time when attacks and the damage they do are on the rise. The FBI’s Internet Crime Complaint Center (IC3) saw over 800,000 complaints and dollar losses related to cybercrime increase by 49% in 2022.
The key difference with SMBs is that their smaller security teams don’t have the same resources and dedicated cybersecurity expertise as larger enterprises. In some cases, smaller teams attempt to enable enterprise-grade security by adopting the same tools as larger organizations. The result is often high licensing costs with few practical benefits.
That’s because traditional enterprise-grade tools aren’t the right fit. Instead of tools built with the Fortune 100 in mind, smaller teams need right-sized solutions that address their security challenges in a way their security teams can support.
The sections below will examine the security challenges facing small and growing teams, how Sumo Logic can address them, and practical use cases.
The challenges facing security teams have changed drastically in recent years. Network perimeters are no longer clearly defined, and attack surfaces are seemingly everywhere. Additionally, with the emergence of DevSecOps, concepts like “shifting left” (which can require teams that weren’t previously responsible for security to integrate it into their work) and human-bot cybersecurity teams have made it so that even the composition of security teams is rapidly changing.
This creates an environment where emerging teams face multiple difficult security challenges. Let’s take a look at exactly what those are.
Modern security teams must account for many users, workloads, applications and deployment models that spread sensitive data across multi-cloud and on-prem environments. Key complexity drivers include:
The complexity of modern IT infrastructure alone often creates silos that limit visibility. For example, applications owned by different business units may not have any central oversight. Similarly, legacy on-prem security tools may not integrate with cloud monitoring tools. Unfortunately, this often leads to a negative feedback loop where more security tools create more complexity.
Cybersecurity is a complex topic with multiple highly specialized areas of expertise. For example, demonstrating compliance with standards like PCI DSS (Payment Card Industry Data Security Standard) or ISO 27001 is difficult without the proper domain knowledge. Similarly, pen testing and identity and access management require specialized skills. The highly competitive cybersecurity job market creates real challenges for organizations that want to hire and retain talented security professionals across different cybersecurity domains.
Smaller teams don’t have the luxury of specialization, meaning they’ll have a tougher time benefitting from traditional enterprise-grade security solutions. Similarly, larger development teams are stretching to prioritize cybersecurity initiatives that weren’t previously their responsibility. Even though these larger teams have more people, they face the same challenges of limited security expertise.
Even when there is a dedicated SOC or team of DevSecOps engineers, it’s easy to get overwhelmed by the sheer volume of thousands of daily alerts and the work involved in truly “shifting left” and supporting the demands of various apps and business units across an organization.
The license costs and operational overhead created by security tool sprawl alone can significantly impact the bottom line. However, that’s far from the only driver of high costs for emerging security teams. The data storage required for effectively detecting threats and compliance audits can also add up fast. Often, this leads to tough trade-offs around data retention policies based on the costs of different storage tiers and deciding which data to ingest due to cost concerns and the fear of surprise overages.
Did you know? According to IDC, the Enterprise DataSphere will grow over twice as fast as the Consumer DataSphere between 2022-2026.
See also: How to Secure Your Cloud Platform and Be Ready for Your Next Audit
Using the tools that Fortune 100 enterprises use makes sense on the surface. After all, they have the expertise to know what works, right? Yes, but knowing what works for them isn’t the same as knowing what will work for your team.
What works for the top one percent of elite security teams will differ from the other 99% of organizations. Buying the tool and hoping a team will grow into it is effectively an aspirational approach to security that isn’t practical or efficient.
For example, an enterprise-grade SIEM is a powerful security solution. But, many organizations don’t need a SIEM at the current stage of their security journey. Investing in a SIEM when you aren’t ready is an excellent example of wasteful aspirational spending.
Sumo Logic Cloud Security Analytics directly addresses this challenge by simplifying — and democratizing — enterprise-grade security for smaller teams. With a right-sized, cloud-native security platform powered by logs, teams can address security and compliance challenges today with the resources they have. And, in a world where security needs to happen now, that can be a game-changer for your security posture.
For emerging security teams that don’t need overly complex tools, Sumo Logic Cloud Security Analytics addresses key security challenges without the higher cost or added complexity of enterprise-grade tooling. Specifically, Cloud Security Analytics helps emerging security teams improve security by:
Taken as a whole, those benefits effectively democratize security and help teams address modern cybersecurity threats without paying for tools that are too complex and expensive for their immediate needs.
See also: Take Control: How To Make the Invisible Serverless Threat Landscape Visible
Now let’s dive into some specific examples of how Cloud Security Analytics can help democratize enterprise-grade security.

Logs and events are essential aspects of observability and threat detection. Centralizing and analyzing logs and events from raw data to actionable information can drastically improve overall security posture. Using Sumo Logic Cloud Security Analytics as a security data lake makes aggregating, storing, and searching your logs and other security data simple and affordable.
Two of the biggest challenges for small teams looking to shift their security tooling to the cloud are the cost of data storage and compliance. The Sumo Logic Cloud Security Analytics solution offers multiple data tiers that provide the flexibility to balance cost and data retention. This data then directly informs the platform’s built-in analytics and threat detection capabilities to help improve overall visibility.
Additionally, Sumo Logic is committed to data security on its platform with compliance attestations and certifications, such as SOC Type II, PCI DSS, HIPAA, GDPR and FedRAMP™ built in.
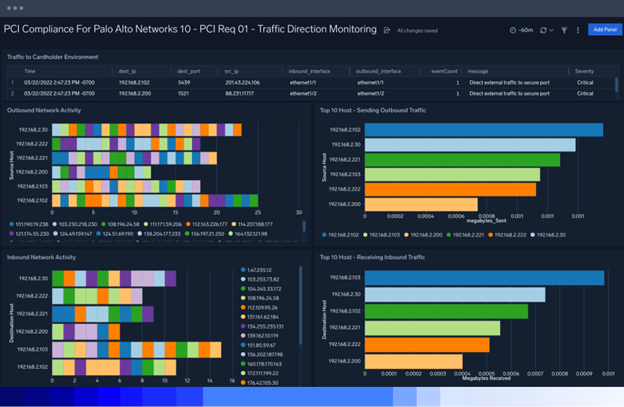
Point-in-time demonstration of PCI DSS compliance can be time consuming, complex and risky. Manual scans and configuration checks go stale quickly. If you only validate compliance during specific point-in-time audits, you risk missing configuration drift and vulnerabilities that emerge between audits.
Continuous compliance monitoring makes it easy and cost effective for smaller teams to maintain and demonstrate PCI DSS compliance on demand.
Cloud Security Analytics also supports continuous compliance readiness monitoring for frameworks like ISO 27001 and CMMC (Cybersecurity Maturity Model Certification).
Modern security teams have to support a wide range of applications. Monitoring every tool in a silo is impractical, so aggregation and centralization of security information are essential. Sumo Logic’s threat intelligence powered by CrowdStrike enables security teams to detect indicators of compromise (IoCs) in near real-time. With hundreds of app integrations that support built-in queries and dashboards, including security tools from Cisco, Okta, Proofpoint, and Zscaler, threat visibility across your environment is easy to acquire.
Configurable alert Monitors and robust operators help you quickly drill down to investigate root causes and remediate issues when a threat is detected.
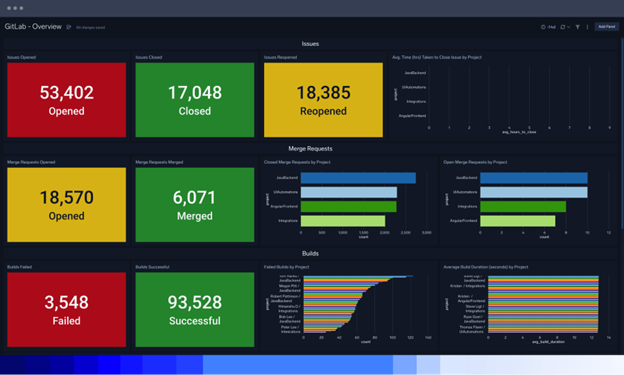
Cloud Security Analytics enables DevSecOps teams to monitor their entire CI/CD pipeline. In addition to integrations with popular DevOps tools like GitLab, GitHub, and Jenkins, the platform can implement robust monitoring and alerting throughout your pipelines. For example, teams can monitor code repositories for malicious access and assess security policy configurations throughout their tech stacks.
>>For a deeper dive on integrating security throughout the software development life cycle, check out our free Accelerate and secure your SDLC with DevSecOps ebook.
With the threats facing modern security teams, aspirational tooling for the one percent isn’t practical. Organizations need solutions that solve problems and prevent threats now with the resources teams have today. That means leveraging tools that address modern threats without breaking the bank or forcing your team to become experts on a specific platform. Additionally, Cloud Security Analytics can grow with your team to support advanced use cases like Cloud SIEM and Cloud SOAR when the time comes.
Sumo Logic’s Cloud Security Analytics solution, powered by logs, helps every team monitor their apps and secure their infrastructure across public cloud, multi-cloud and on-prem environments. To see what our cloud-native security platform can do for you, sign up for a free 30-day trial today!
Property of TechnologyAdvice. © 2026 TechnologyAdvice. All Rights Reserved
Advertiser Disclosure: Some of the products that appear on this site are from companies from which TechnologyAdvice receives compensation. This compensation may impact how and where products appear on this site including, for example, the order in which they appear. TechnologyAdvice does not include all companies or all types of products available in the marketplace.